AI-based phishing simulation
Simulated phishing attacks directly in your employees' inbox. Adapted to each employee for the optimal learning experience.
Simulated phishing attacks directly in your employees' inbox. Adapted to each employee for the optimal learning experience.
Your biggest security risk is the e-mails your employees receive. Train your employees to identify phishing and minimize that risk.
Phishing is a constant threat to all companies, so it’s important to train the employees in identifying and averting advanced phishing attacks. Continuous focus on phishing increases and maintains awareness, while naturally becoming a part of the employees' daily lives.
Our phishing simulations are sent out on an ongoing basis so that the employees are always ready to protect themselves and the company from cyberattacks.
Our AI-based phishing simulations are tailored to each individual employee. We identify the employees who pose the greatest security risk and ensure that they receive the most training.
We focus the training where it’s needed the most. This way, we make sure that all employees receive the optimal amount of training without it taking up too much of their time.
The onboarding only takes 15 minutes and then the company is all set to receive the simulations. Our outsourcing solution automatically onboards new employees on an ongoing basis.
After the onboarding, our security experts handle all communication to the employees, and there are no administrative tasks for the company.
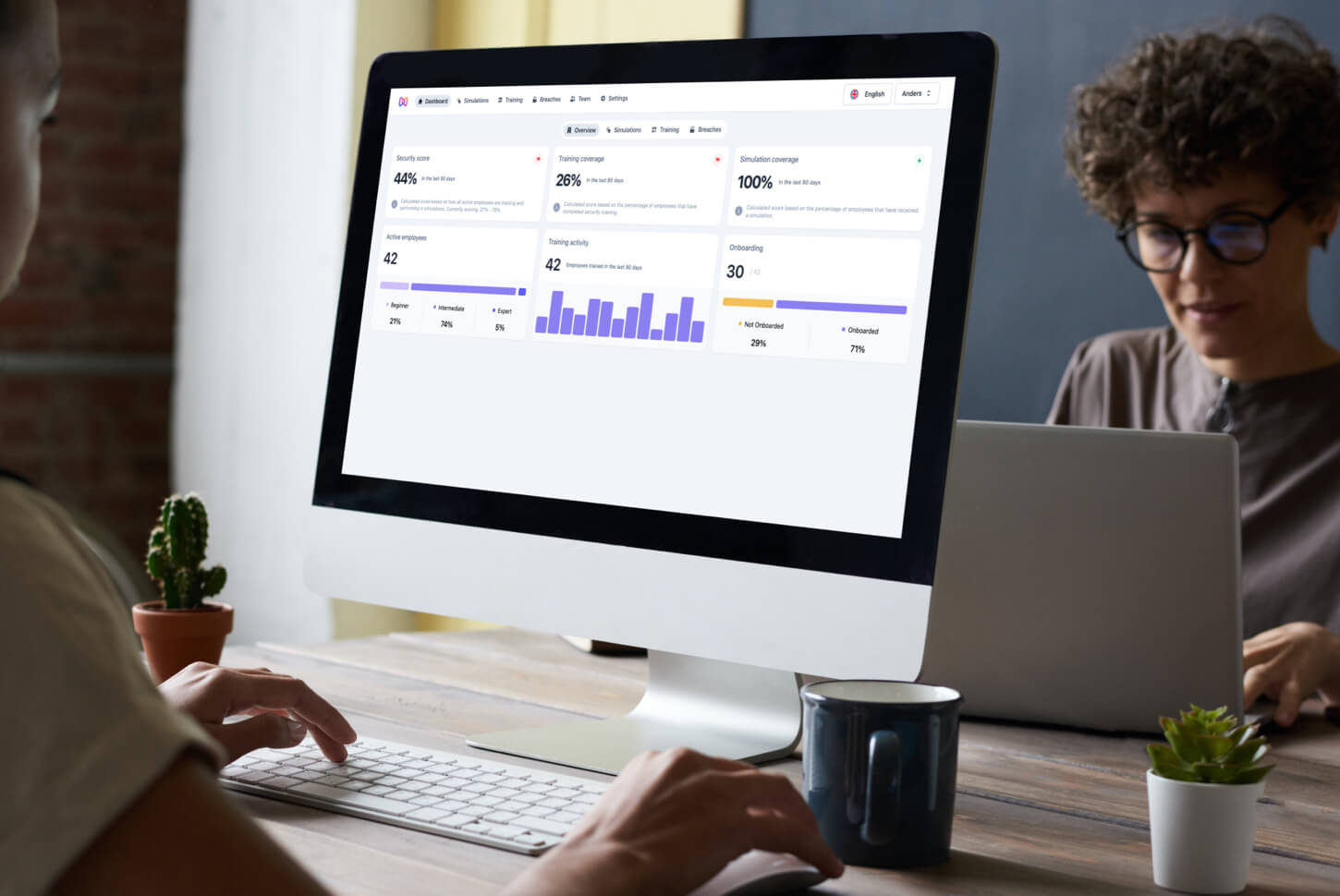
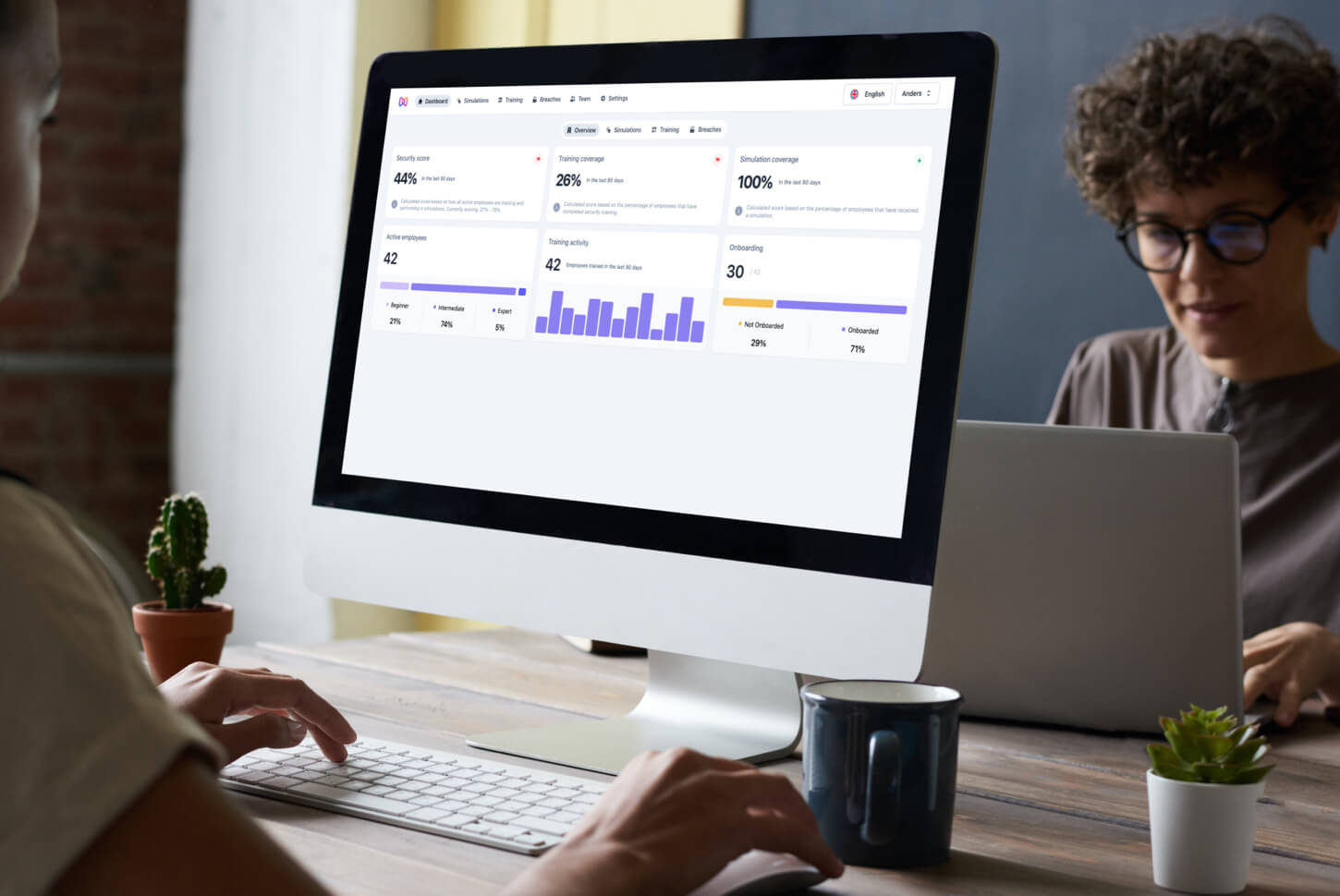
Discover how Moxso's features can assist you.
With our add-in, employees can report phishing directly in their inbox with a single click.
Baseline test
Get an overview of the company's current risk level with a baseline test.
Monthly reporting
We send the company a report on the employees' progress every month, both at individual and departmental level.
Tailor-made campaigns
We set up phishing campaigns specifically designed for key employees in the company.
Attacks of all kinds
Our comprehensive catalog of phishing e-mails cover many types of phishing, including spear phishing and CEO fraud.
Realistic simulations
The phishing simulations mimic real phishing attacks and incorporate strategies from social engineering.
Natural culture change
Our continuous phishing simulations strengthen the cybersecurity culture of the company.

“After using Moxso for just a couple of months we saw a huge difference in our employees’ habits and attitude towards cybersecurity. We chose Moxso because they offer an outsourcing solution that removes all administrative tasks on our end.”
Anders van Dhürbourgh-Jacobsen
CFO - Damvad Analytics

Hackers try to target your employees through phishing attacks. If they succeed, it can have huge consequences for the security of your organization.
In this white paper you will learn:
How to increase efficiency with dynamic simulations
How to save time and resources with automated and continuous simulations
Everything you need to know
After contacting Moxso, you will receive a personal demo from one of our security experts. The demo shows you how the phishing simulations work and gives you access to try out the e-learning hub, where you will also find the overview of employees' leaked personal information in external data breaches.
Moxso then imports the employees from the company's active directory. Moxso can import employees from Microsoft, Slack and Google Workspace. When we import employees, we only get reading access to the relevant employee data.
Moxso is then whitelisted in the company's spam filter, so you can be sure that all the simulations reach your employees' inboxes.
The first simulations we send out are a part of your baseline test. The baseline test aims to measure your company's current ability to identify phishing and determine which employees pose the greatest security risks.
After the baseline test, all your employees will be introduced to Moxso's phishing and awareness training as well as data breach monitoring, and they will get access to the e-learning hub.
Phishing scams are the most widespread and common cyberattack worldwide and billions of phishing e-mails are sent out every day.
Phishing is a malicious attempt to defraud individuals of their information or cause them to take certain actions. Scammers try to obtain confidential information or sensitive data, such as login credentials, credit card numbers, account numbers, or other financial information, home addresses, social security numbers etc.
This personal information can be used by the criminals to steal money from bank accounts, commit identity theft, carry out other cyberattacks, or they can sell the information to other cybercriminals.
Phishing can be carried out via e-mail, text messages, or over the phone. Phishing via text messages is called smishing (SMS phishing) and phishing through phone calls is called vishing (voice phishing). The most common phishing scam is carried out as e-mail phishing attacks. These e-mails are allegedly sent from a trustworthy entity or someone the recipient personally knows or trusts. It can be public authorities, financial institutions, family, friends, etc.
The content of the message is often that the recipient has to log onto an account, change a password, pay a delivery fee, or transfer money. The message also states that the recipient must respond quickly. The message contains either a malicious link or an attachment.
If the recipient clicks on the link, they will be led to a phishing website where they have to enter their information. As soon as the recipient enters their personal details or sensitive information on the malicious website, the information will be sent to the cybercriminals. If the recipient clicks on the attachment, he/she will unintentionally download malware to their computer.
If an employee in your company has once been defrauded of their information or has transferred money to an offshore account, it can be difficult to minimize the damages. This can result in data loss, financial loss, loss of customers, damage to company reputation, and more.
The vast majority of cyberattacks start with phishing, notably ransomware attacks, and by training your employees to identify phishing, your business can build a strong defense against cyber threats.
The best way to prevent phishing attacks is to educate your employees on phishing awareness.
Moxso has designed a “Report Phishing” add-in that enables your employees to report phishing e-mails directly in their inbox. Our add-in is added to your e-mail client when your company onboards.
When an employee wants to report suspicious emails as phishing, they click on our add-in, which is a button with our logo on it. After they click on the add-in the following happens:
No, Moxso's simulations are dynamic and adapt to each employee's security level. The simulations are AI-based, and the frequency of simulations is calculated by special algorithms.
Employees who pose a major security risk, ie. employees who often click on links in the simulated phishing attacks, receive more simulations than the employees who rarely click.
This means that your employees receive different phishing simulations at different times and on different days.
The custom simulations not only create the best learning paths for every one of your employees, but they also mimic real phishing attacks, as hackers often create specific phishing e-mails for specific people.
The traditional form of mass phishing, where a large number of generic e-mails are sent out in bulk, is primarily directed at private individuals. Employees in companies are most often affected by spear phishing, which is specifically targeted at them.
Cybercriminals research employees in a company, typically using social media and Google to find personal information, and they create targeted phishing e-mails, cleverly choosing the supposed sender, the content, and the time of delivery. This makes the phishing attack much more difficult to recognize and there is a greater chance that the recipient will be fooled.
By making our simulated phishing e-mails as realistic as possible, we create the best learning conditions for your employees to identify various types of phishing e-mails.
Yes, you can get company-specific phishing simulations that ensure that your employees can handle advanced socially engineered phishing attacks targeting your particular business.
Moxso has a large catalog of different phishing e-mails with varying degrees of difficulty, themes, and strategies from social engineering.
We can put together a specific catalog for your company, which contains phishing e-mails that are targeted at your employees, the internal work and communication structure, the external communication structure, the use of IT tools, the use of social media etc.
The simulations are adapted to match an employee's cybersecurity behavior. Initially, the security risk that an employee poses is calculated based on the results of the baseline test.
Moxso observes each employee's reaction to the simulations in the baseline test, ie. whether they open the e-mails and whether they click on links or try to open attachments in the e-mails.
The content and frequency of the simulations are determined by how large a security risk an employee poses to your company. If an employee poses a major safety risk after the baseline test, they will regularly receive simulations whose difficulty matches their level.
The simulations will continuously adapt to each individual employee. If an employee becomes better at identifying the simulations as phishing, they will start receiving fewer simulations. The simulations will however be more advanced and have a higher degree of difficulty.
The dynamic simulations ensure that all your employees get the right number of simulations, and the customized level of difficulty creates the optimal learning path.
All companies can fall victim to cyberattacks, and it's therefore important that a company, regardless of size or industry, trains its employees in the field of cybersecurity.
Moxso therefore designs simulations for companies of all sizes and for all kinds of industries.
Moxso tailors the simulations based on the size of your company, including the number of employees and departments and compiles a specific catalog of phishing e-mails.
Moxso also tailors the simulations based on industry-relevant IT tools and industry codes. Moxso continuously runs statistics on the types of phishing e-mails that target specific industries and continuously adapt our catalogs of phishing e-mails to suit your particular industry.
Spear phishing is a phishing method that targets specific individuals or groups within an organization. It's a targeted and more advanced method of phishing, a malicious attack which uses e-mails, social media messages, text messages, and other platforms to trick users and to get them to give away personal or sensitive data or perform actions that cause systems compromise, data loss, financial loss, and more. While mass phishing attacks may rely on spray and pray methods that deliver mass e-mails to random individuals, spear phishing focuses on specific targets and involve prior research.
A typical spear phishing attack includes an e-mail with an attachment. The e-mail includes information specific to the target, including the target's name and position within the company. This social engineering techniques used increases the chances that the victim will believe that the e-mail is legitimate and preform the desired actions, for example transfer money or give access to company data.
Spear phishing emails are typically used in targeted attack campaigns to gain access to an individual’s account or impersonate a specific individual, such as a ranking official or those involved in confidential operations within the company.
Spear phishing hackers use reconnaissance methods before launching their phishing campaigns. They might gather several out-of-office notifications from a company to determine how they format and structure their e-mail addresses. They often also use social media and other publicly available sources to gather information, they can use to make personalized e-mails.